The paper titled “Bluetooth Low Energy Mesh: Applications, Considerations and Current State-of-the-Art” by researchers in Australia provides a comprehensive review of Bluetooth Mesh technology, focusing on its applications, challenges and opportunities in the context of the Internet of Things (IoT).
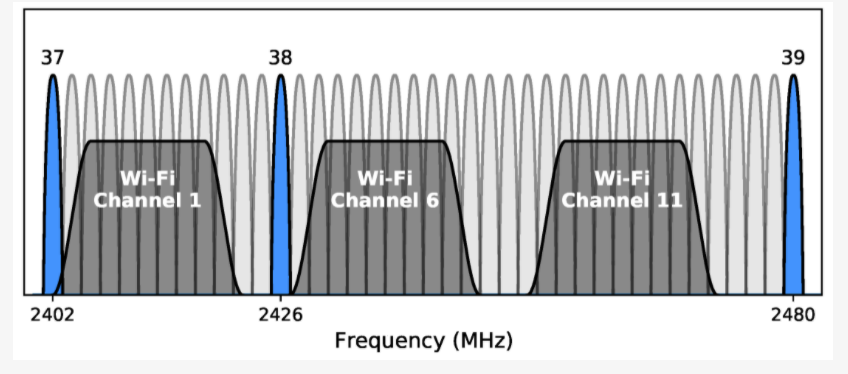
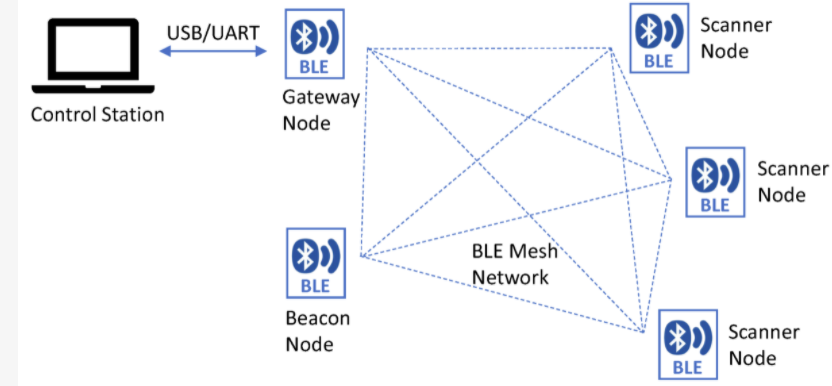
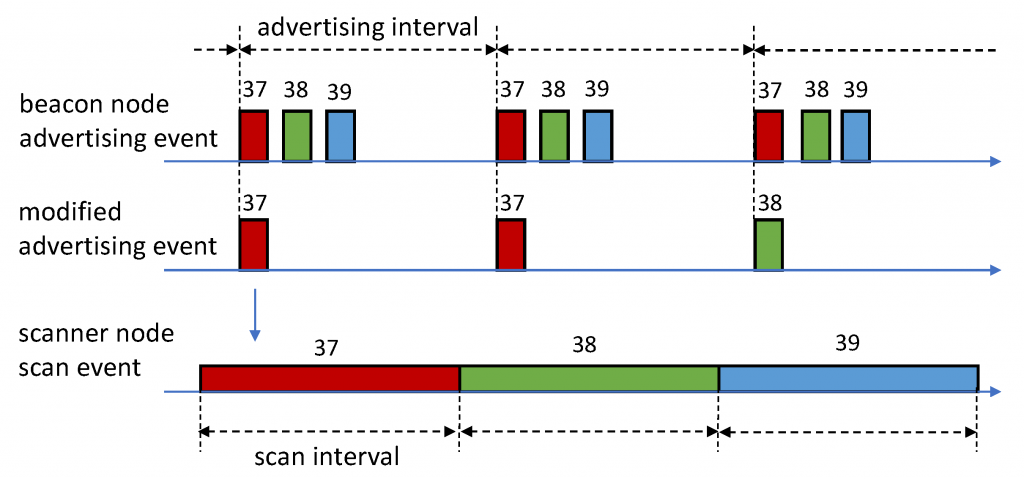
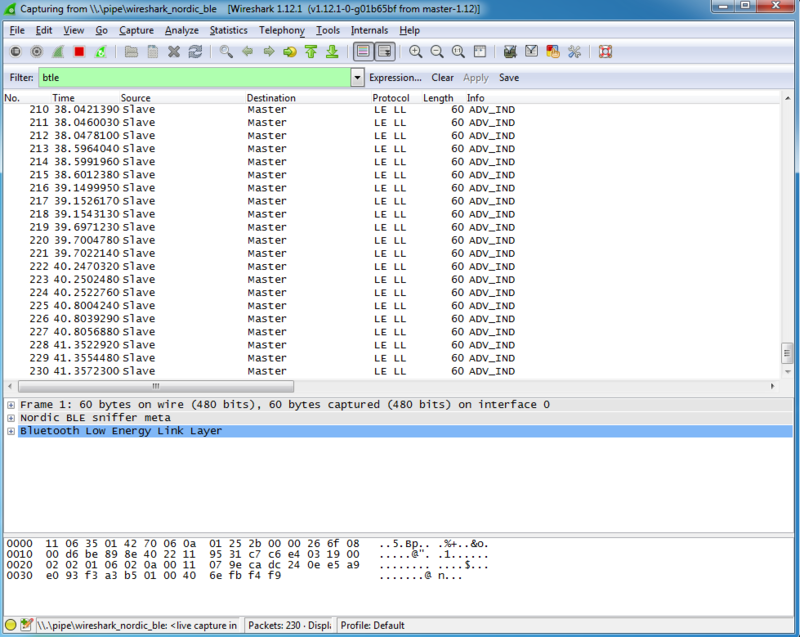
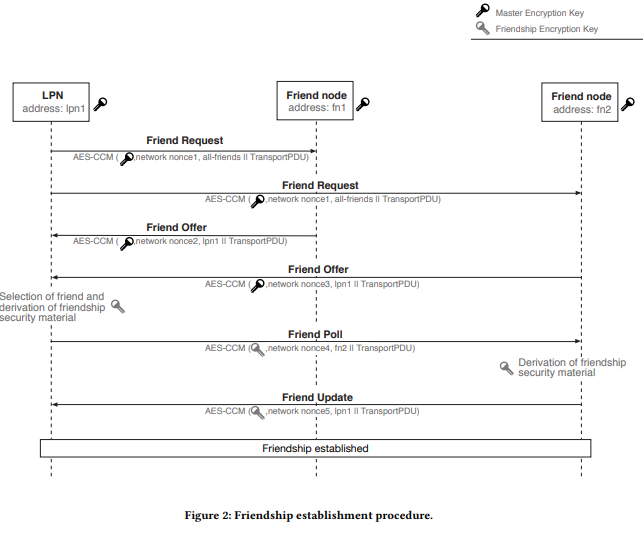
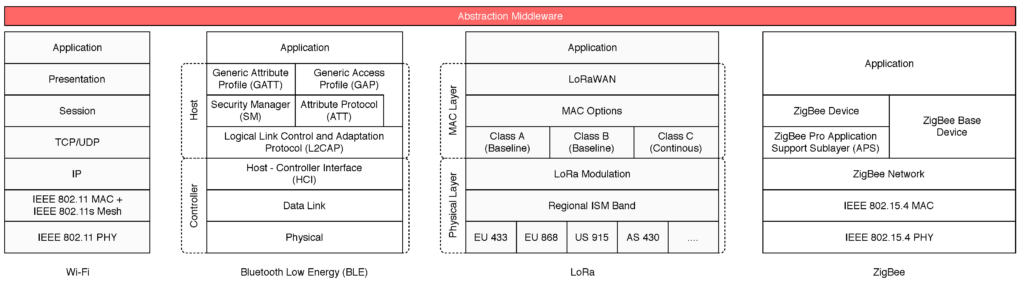
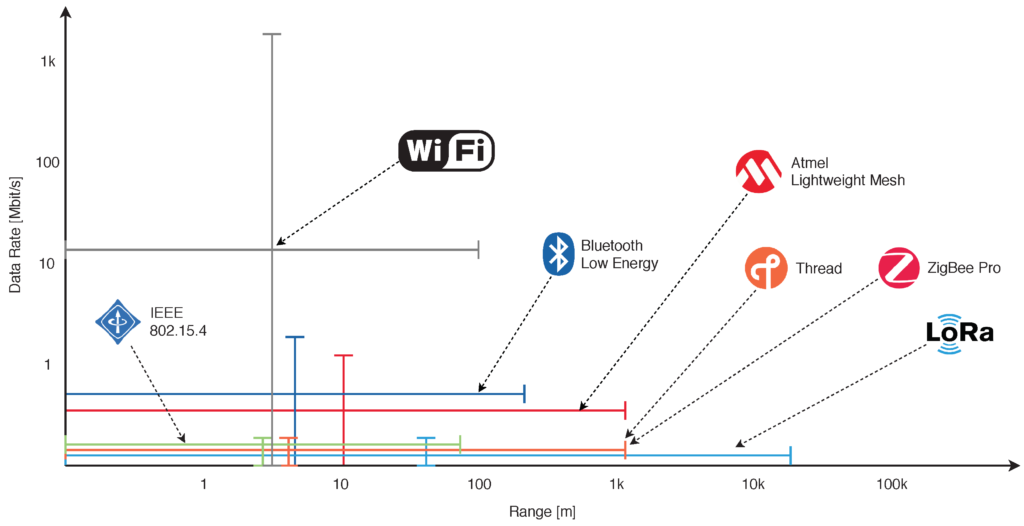
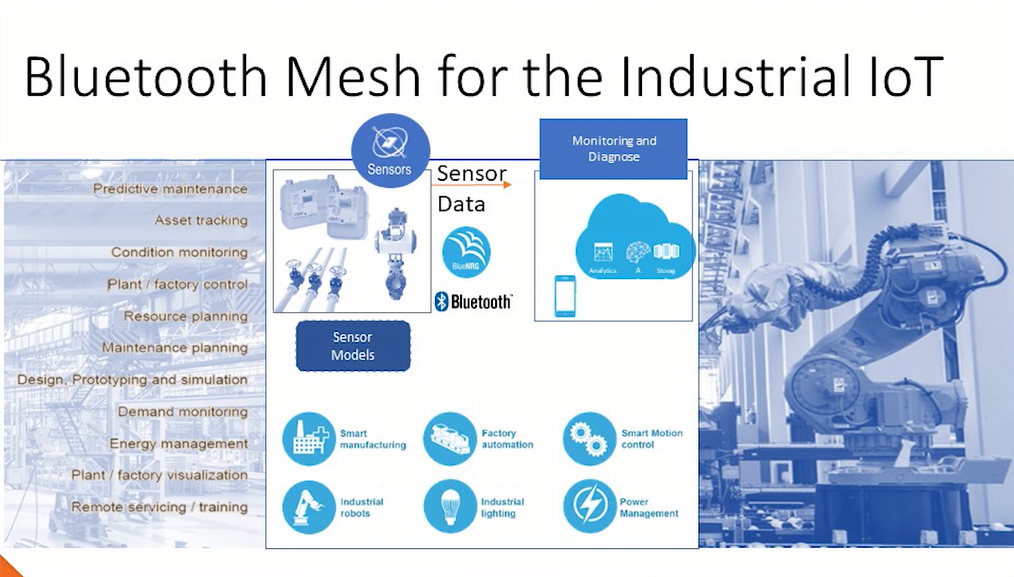
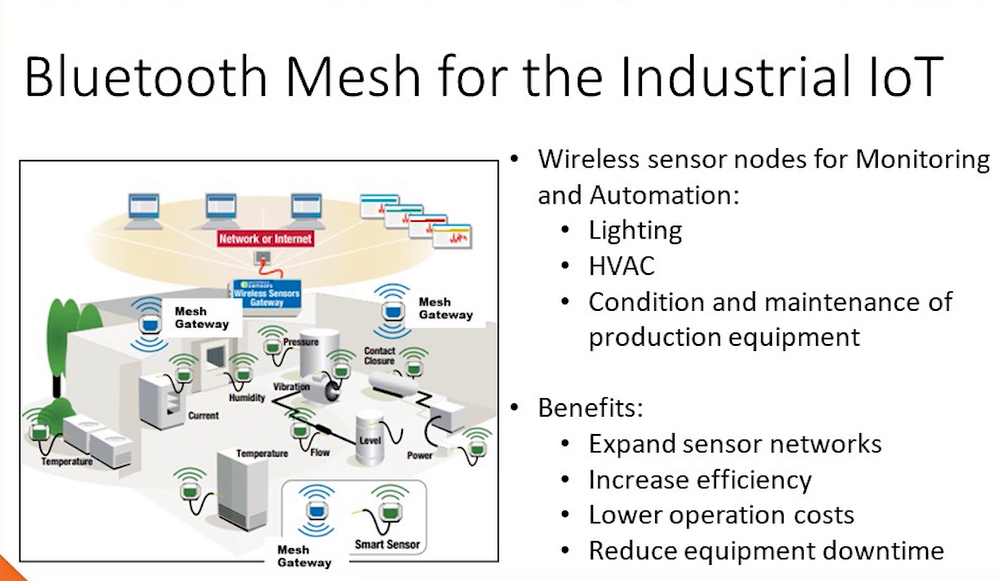
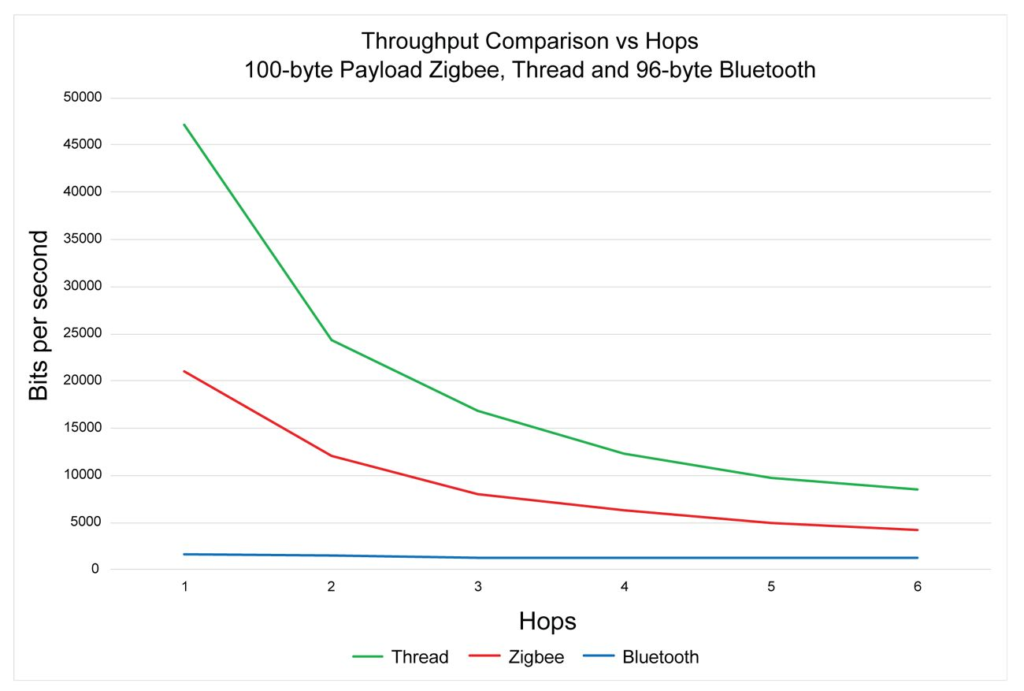
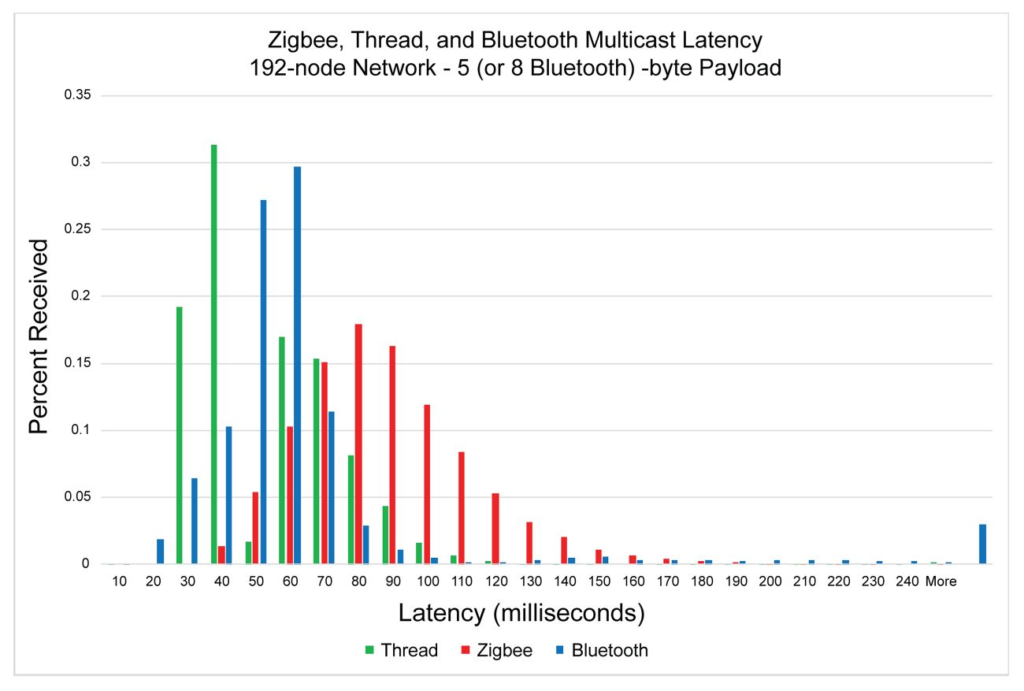
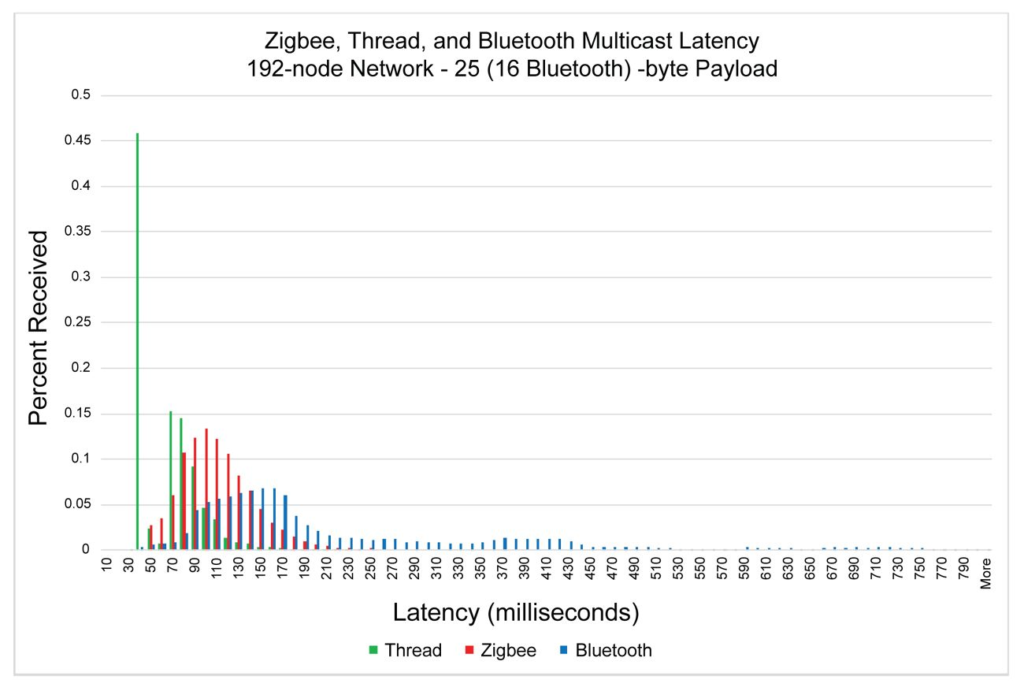
The study begins with an overview of Bluetooth Mesh, detailing its protocol stack, node types and real-life implementation. It further explores the suitability of Bluetooth Mesh for IoT applications, considering factors like scalability, flexibility, robustness, responsiveness, security, and energy efficiency. A comparison with other communication technologies such as Wi-Fi, Z-Wave, Zigbee, and LTE-M is also provided to highlight the pros and cons of Bluetooth Mesh.
The paper includes a review of research published between 2017 and 2022, since the official release of Bluetooth Mesh by the Bluetooth Special Interest Group (SIG). It also presents experimental investigations and insights from a test-bed, analysing real-world implications for latency, energy, scalability, and reliability based on Bluetooth Mesh parameters and behaviour.
One of the key findings is that Bluetooth Mesh is an emerging technology that can support reliable communications in IoT environments. However, the performance of the Bluetooth Mesh network can be significantly influenced by parameters and functions such as time-to-live (TTL) and relay features. The configuration and selection of these parameters can affect reliability and energy consumption, indicating that further experimental work is needed to understand these effects.
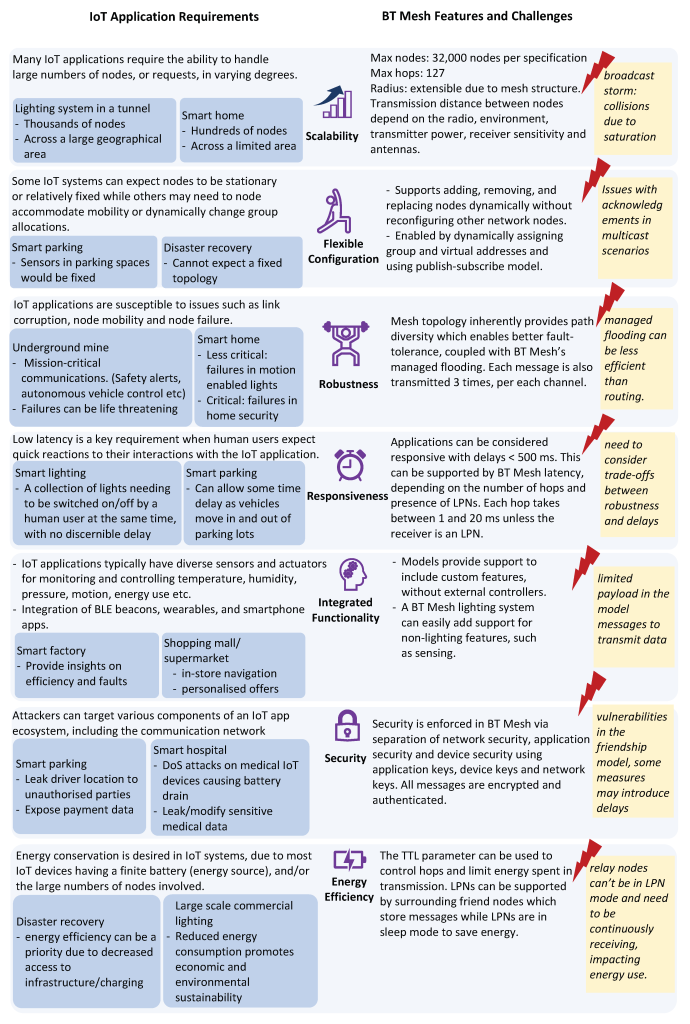
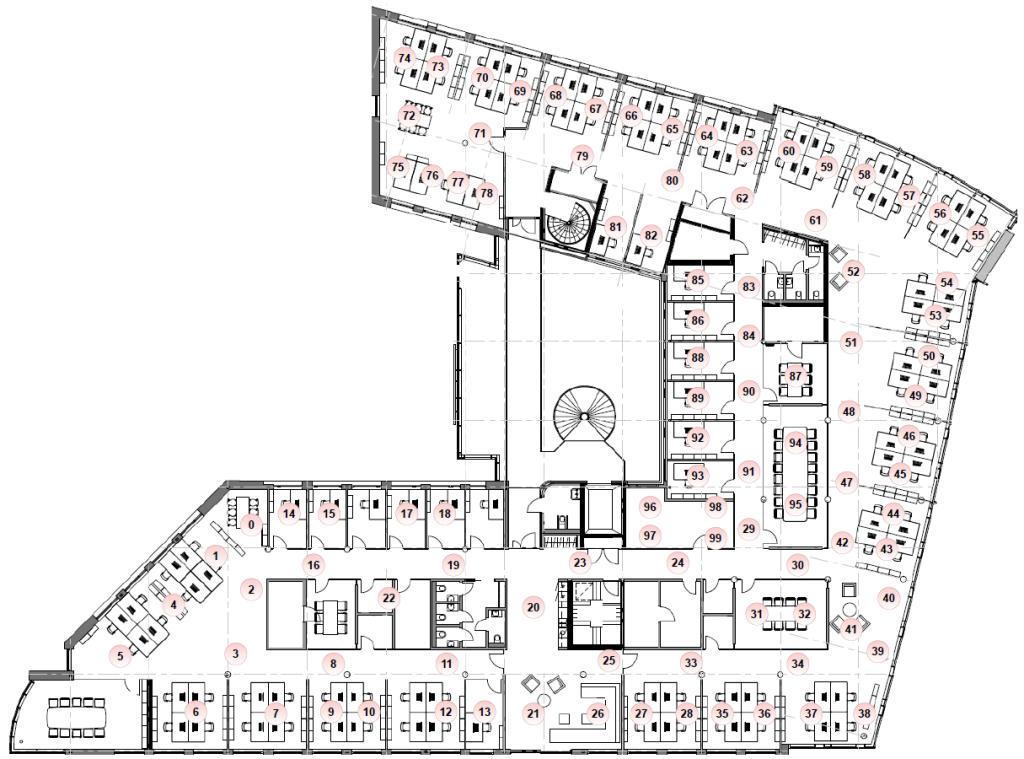
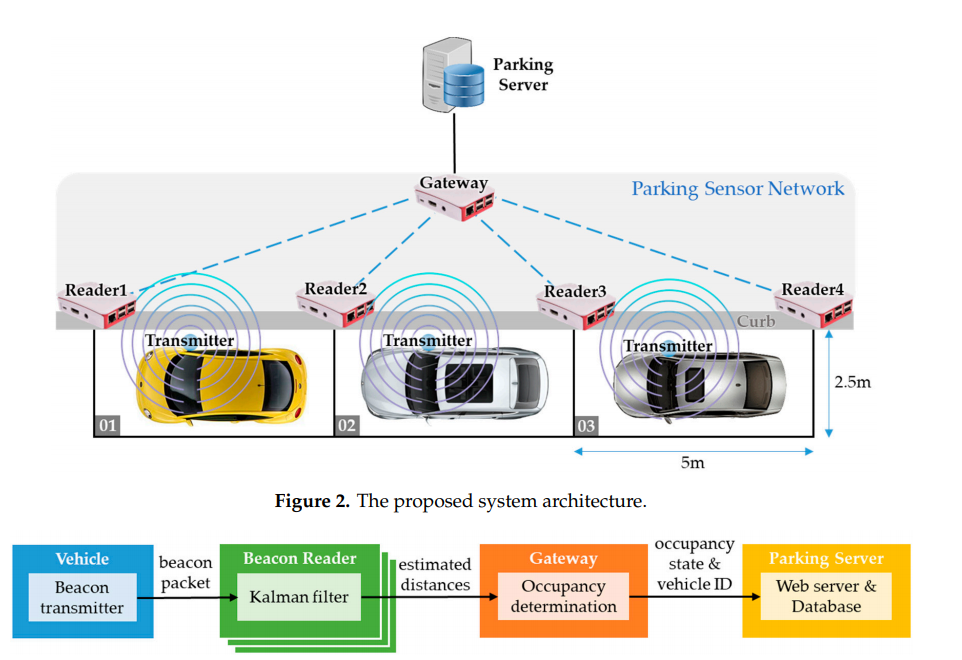
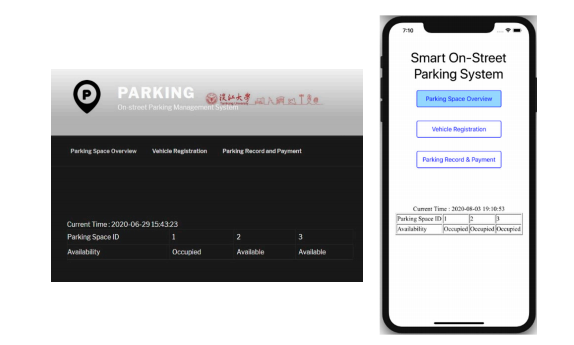
The paper also discusses the practical applicability of Bluetooth Mesh for interconnecting nodes within close range or performing proximity sensing and localisation for limited bandwidth operations.
The paper recognises Bluetooth Mesh as a promising technology for various IoT applications but acknowledges that much work remains, particularly in understanding the impact of different parameter settings and in exploring its robustness in different mobility situations.