There’s lots of information on Bluetooth beacon security, Bluetooth attacks and using beacons to track individual user data but these are known, small risks we might expect. What about unknown things such as espionage?
Recently, a prospective customer posed a different question: How can we ensure that purchased beacons are not engaging in activities beyond their intended purpose, such as eavesdropping or transmitting sensitive information? This question becomes even more pertinent when considering beacons manufactured overseas that might be deployed in sensitive locations.
Typically, a single SoC chip on the beacon’s simple Printed Circuit Board (PCB) is responsible for all operations. Upon examination, if there are no additional, unexpected, chips on the PCB, it limits the beacon’s ability to perform unexpected tasks. If the hardware is not compromised, the only factor to consider is the standard, usually Nordic Semiconductor, System on Chip (SoC) used in the beacons. This means that any potential spying would likely be restricted to software in the SoC rather than hardware modifications.
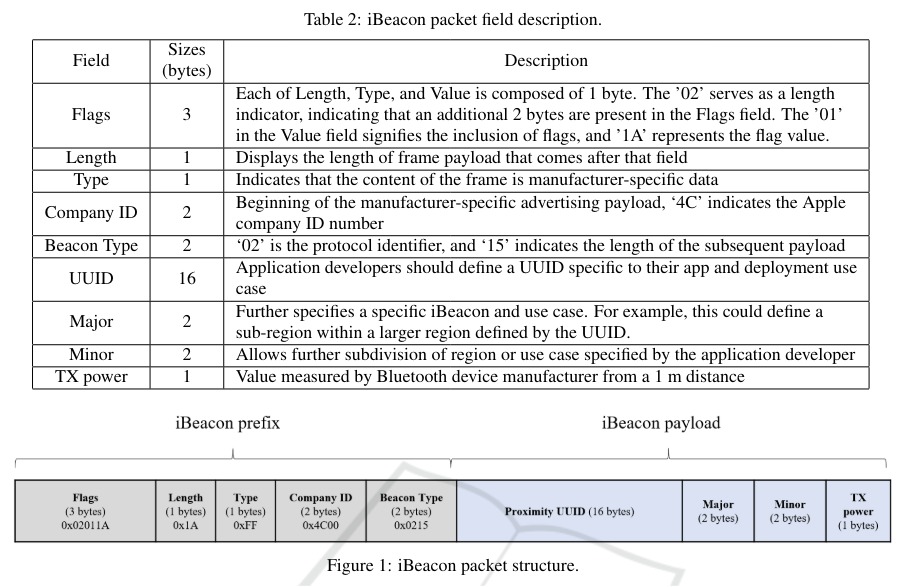
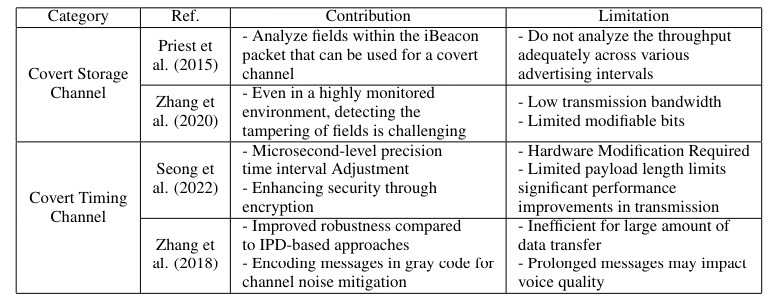
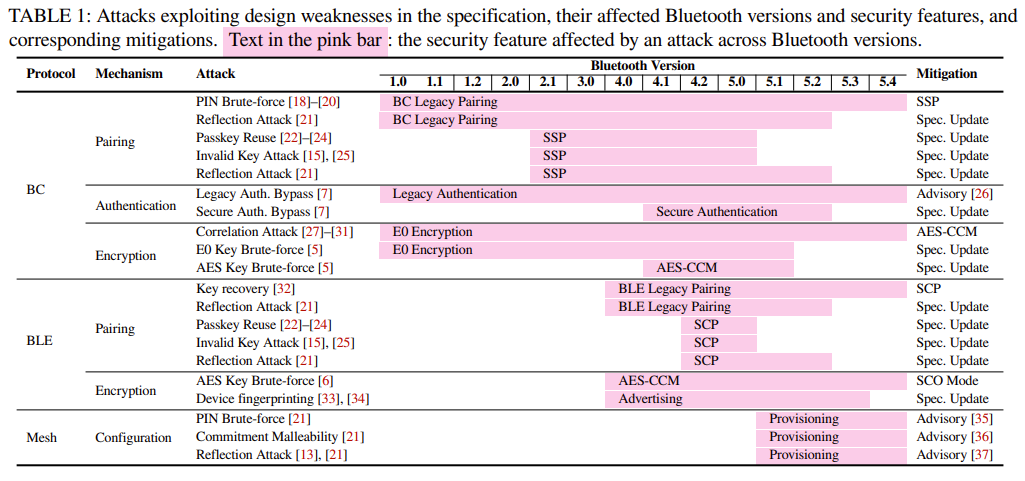
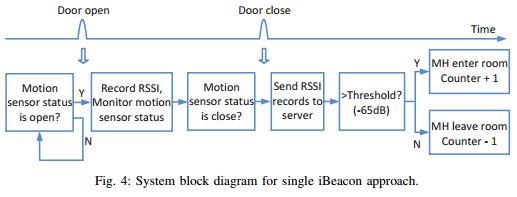
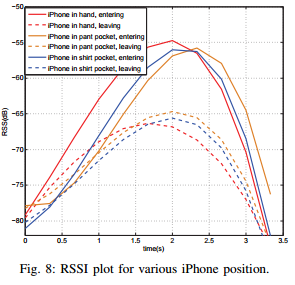
Let’s assume beacons can only exploit the capabilities that the standard SoC chip provides. These usually include Bluetooth, ANT, 802.15.4 and other proprietary and non-proprietary 2.4GHz protocols. Crucially, beacons are designed primarily to send signals rather than receive them. They transmit signals every millisecond, typically every 200ms to 1000ms, to maintain low battery consumption. For a beacon to listen or scan for information, it would require significantly more power, thus drastically reducing battery life. Similarly, relaying, perhaps via covert channels, any gathered information would also deplete the battery swiftly. Therefore, any huge deviation from the expected battery life could be a tell-tale sign of unauthorised activities.
Given that beacons usually only send data, they cannot capture sound or video without additional, noticeable components. When they are listening using the protocols they are designed for, the information they could gather would be limited and lack context, such as identifying what they have seen or the specific location.
While the theoretical possibility of beacons being used for spying exists, it is easily detectable due to the easily examined, simple hardware, limited capabilities of the SoC and the significant power requirements for any additional activities. By understanding the simplicity, limitations and functionalities of these devices, businesses can better safeguard against potential espionage.
Read about our consultancy for more advice